Technology Roadmaps: A More Secure Environment
Data Fusion for Threat Detection
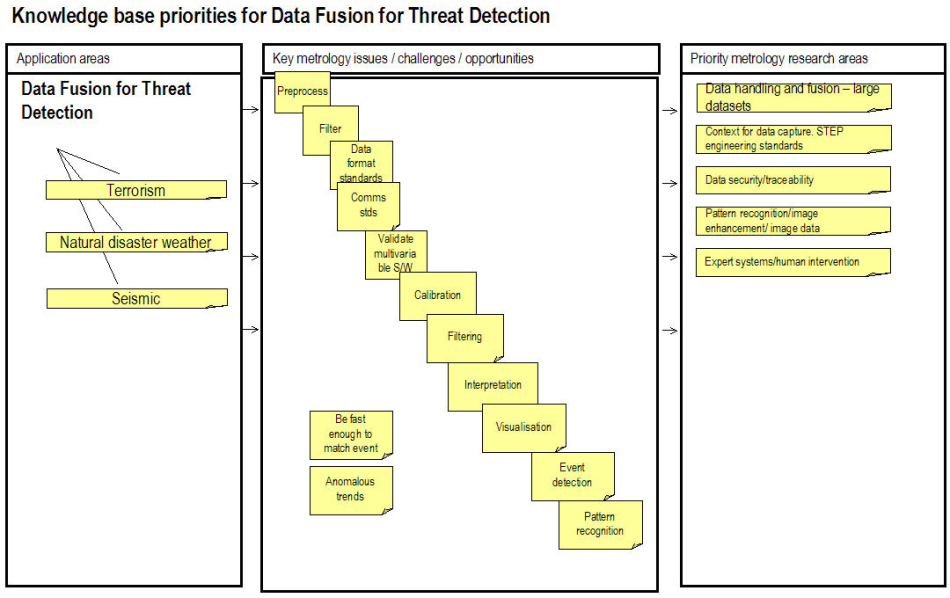
The diagram below further explores the knowledge base priorities. The subject is split out into the key application areas each of which is tracked through the key challenges, opportunities and gaps in the knowledge base and prioritised into key research areas.
If you feel that this document has omissions, or if you disagree with what has been included, please let us know via the feedback form